Table of Contents
ToggleIn an era where technology has seamlessly integrated into every facet of our lives, the importance of safeguarding our digital landscapes cannot be overstated. Cybersecurity threats loom large, targeting unsuspecting organizations of all sizes. This article delves into why cybersecurity awareness in the workplace is not just necessary but critical, highlighting how informed and vigilant employees are the first line of defense against potential breaches.
Understanding Cybersecurity Threats
Cybersecurity threats are not just frequent but also increasingly sophisticated, exploiting both technological vulnerabilities and human psychology. The landscape of cyber threats includes a variety of attacks that can cripple organizations in profound ways.
- Phishing attacks are deceptively simple yet effective, leveraging social engineering to deceive recipients into revealing personal information or downloading malware. These attacks are often done via seemingly legitimate emails or messages, skillfully mimicking trusted sources to lure victims into a trap.
- Malware, short for malicious software, includes viruses, worms, trojans, and spyware. It can disrupt or damage a system’s operations, steal sensitive data, or covertly take control of entire systems. The consequences can range from annoying pop-ups to serious financial and data losses.
- Ransomware is a particularly malicious type of malware that locks real users out of their systems or encrypts their data, demanding a ransom payment to restore access. The rise of cryptocurrencies has exacerbated this threat by making transactions difficult to trace.
Table: Types of Cyber Threats and Their Impact
| Threat Type | Description | Potential Impact |
|---|---|---|
| Phishing | Deceptive emails or messages to extract data | Identity theft, unauthorized access |
| Malware | Software designed to harm or exploit systems | Data loss, system damage, operational disruption |
| Ransomware | Malicious software that demands a ransom | Data hostage, financial loss, reputation damage |
Dr. Alice Johnson, a cybersecurity expert, emphasizes the dynamic nature of these threats: “As technology evolves, so do cyber threats. They are becoming more adaptive, finding new vulnerabilities to exploit. It’s a perpetual arms race, and staying informed is as crucial as implementing robust cybersecurity measures.”
The Human Factor: Cybersecurity’s Weakest Link
Human error remains a significant cybersecurity vulnerability, often cited as a leading factor in breaches. A staggering 85% of breaches involve a human element, according to Verizon’s 2021 Data Breach Investigations Report. This statistic underscores the critical weaknesses in cybersecurity arising from inadequate technology and human mistakes.
The susceptibility to errors is largely due to a lack of awareness. Employees may not recognize the signs of a phishing email or might choose simple, easily guessable passwords due to convenience. Each of these decisions opens a door to potential attacks. For example, an unsuspecting click on a malicious link can install malware that compromises an entire corporate network.

Continuous education and industry-recognized cybersecurity or IT Security training play a pivotal role in mitigating these risks. Regular training sessions on industry-recognized certification programs like COBIT 2019 Foundation, which acts as an entry-level certification for IT professionals in an organization, can dramatically improve employees’ ability to identify and respond to cyber threats. Simulated phishing exercises, for instance, help individuals recognize the subtleties of fraudulent requests by exposing them to mock scenarios in a controlled environment. Additionally, workshops focusing on best password creation and data handling practices further equip staff with the knowledge needed to navigate the digital workplace safely.
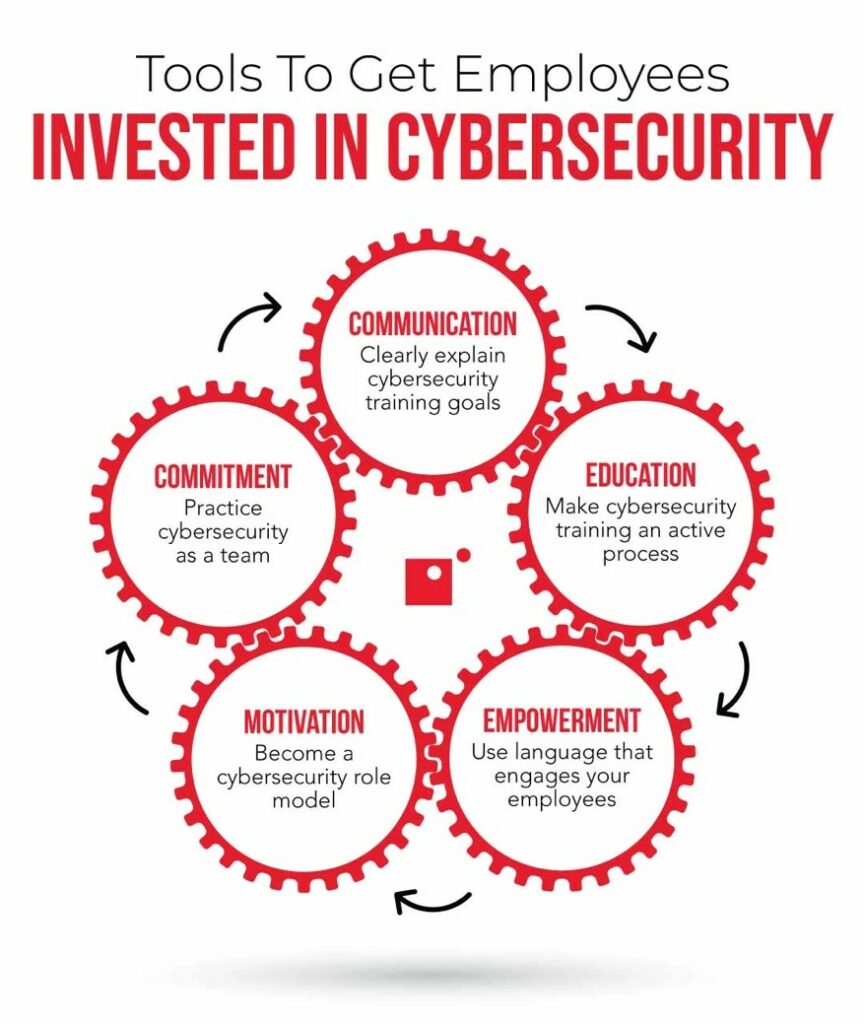
Building a Culture of Cybersecurity Awareness
Creating a culture of cybersecurity awareness starts at the top. When top leaders emphasize the importance of security, it sets a precedent throughout the organization. Regular IT Security training sessions, updates on the latest threats, and clear communication on security protocols are essential. These efforts ensure every employee understands their role in protecting the company’s digital assets. Here’s how organizations can achieve this:
Steps to Cultivate a Cybersecurity-Aware Workplace Culture
Table: Steps to Cultivate a Cybersecurity-Aware Workplace Culture
| Step | Description |
|---|---|
| Define Clear Cybersecurity Policies | Establish and enforce clear guidelines on how employees should handle sensitive information and respond to security threats. |
| Regular Training and Simulations | Conduct ongoing cybersecurity training and simulations to keep security top of mind and ensure employees can recognize and react to threats effectively. |
| Promote from the Top | Encourage senior management to demonstrate their commitment to cybersecurity, which reinforces its importance across the organization. |
| Foster Open Communication | Create channels for employees to report suspicious activities without fear and share updates on new threats and security practices. |
| Reward Compliance and Vigilance | Recognize and reward employees who acknowledge and adhere to security policies and those who proactively protect the organization’s digital assets. |
Role of Leadership in Promoting Cybersecurity
Leadership plays a crucial role in promoting a culture of cybersecurity. Leaders must not only endorse but actively participate in cybersecurity initiatives. By discussing cybersecurity in meetings, sharing stories related to security breaches, and visibly following security protocols, leaders can set a powerful example for the entire organization. Leadership involvement at every level, from the CEO to middle managers, helps to embed cybersecurity into the corporate ethos, making it a standard part of operations rather than an afterthought.
Benefits of Regular Awareness Sessions and Updates
Regularly scheduled awareness sessions keep cybersecurity front of mind for employees and provide the latest information on emerging threats and defensive tactics. These sessions serve as a reminder of the protocols and help employees feel more prepared to act in a timely and informed manner when potential threats arise. Updates can also serve to continuously evolve the organization’s cybersecurity strategies in line with the latest technologies and threat landscapes.
Case Study: Cyber Attack at XYZ Corp
- Background: XYZ Corp, a mid-sized financial services firm, had basic security measures in place but needed a robust training program for its staff.
- Incident: A sophisticated phishing attack targeted several employees, leading to unauthorized access to confidential client data.
- Response: The IT team quickly isolated the compromised systems and mitigated further damage. Communication with affected clients was immediate, transparent, and handled with care.
- Outcome: Despite swift actions, the attack resulted in significant data loss and a tarnished reputation.
- Lessons Learned: Post-incident, XYZ Corp overhauled its cybersecurity strategy, implementing regular training and simulated phishing exercises to test employee awareness.
The Role of Cybersecurity Training and Certification
For IT staff, understanding the nuances of cyber threats is paramount. Certifications such as Certified Information Systems Auditor (CISA), Certified Information Security Manager (CISM), and Certified in Risk and Information Systems Control (CRISC) equip professionals with the necessary skills to anticipate and mitigate risks effectively. These certifications are not just letters after one’s name; they are a testament to a professional’s ability to safeguard an organization against complex threats.
These globally recognized certifications ensure that professionals are up-to-date with the latest security practices, technologies, and regulations, which is crucial in a field that evolves as rapidly as cybersecurity. Certified professionals bring a higher level of expertise and understanding, which significantly enhances the security posture of their organizations.
Table: Benefits of Certified Cybersecurity Professionals
| Certification | Benefits |
|---|---|
| CISA | Enhances skills in information system auditing, control, and security. |
| CISM | Focuses on managing, designing, and overseeing an enterprise’s information security. |
| CRISC | Provides expertise in managing risks and implementing information system controls. |
Organizations that invest in certified professionals see a marked improvement in their cybersecurity measures. These credentials not only raise the standard of security practices but also instill a greater sense of confidence among stakeholders, knowing that their data is handled by experts trained to thwart cyber threats effectively.
Conclusion
Cybersecurity is not just an IT issue but a business imperative. Through education and training, organizations can significantly diminish the risk of cyber incidents. As the digital landscape evolves, so too should our defenses. Investing in certified cybersecurity training programs is not merely beneficial; it is essential for survival in this digital age.
This article serves as a reminder of the pivotal role cybersecurity awareness plays in maintaining not just security but also the trust of clients and the integrity of our digital world.
